Maintaining enterprise security only gets more difficult, as additional means of cyberattack and increasingly sophisticated techniques are added to attackers’ arsenal.
“Our personal and professional attack surfaces have never been greater, and they are only expected to grow as organizations and individuals continue to increase their reliance on the digitally connected world for a variety of tasks,” explained researchers from network infrastructure and security services company Verisign. “Security practitioners must not only protect their enterprise assets, but also guard against threats to their supply chain and other business ecosystems.
These threats, coupled with the cyber threat landscape’s continuous evolution in terms or actors, tactics and motivations, have created a situation where organizations must now move toward an intelligence-driven, holistic security approach to keep pace with the rapid changes in attackers’ tactics, techniques and procedures (TTPs).”
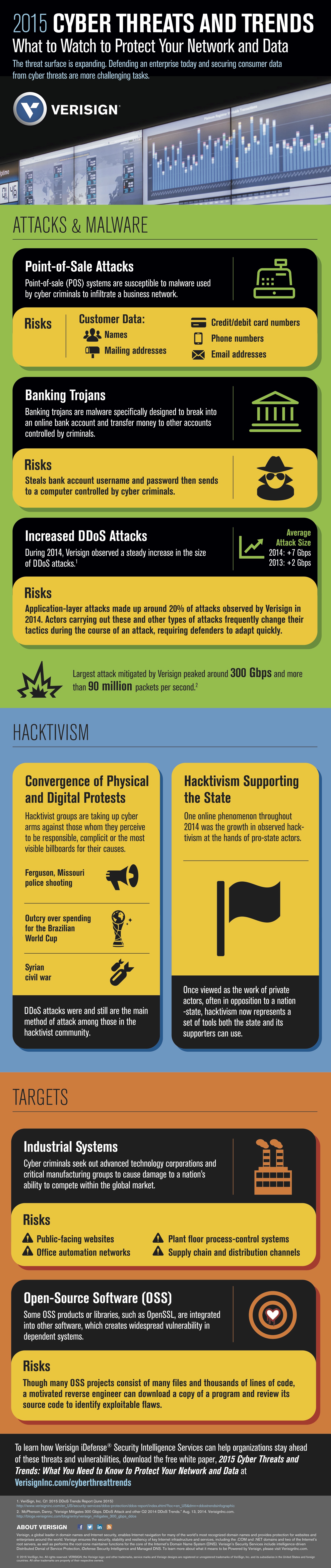
According to Verisign’s “2015 Cyber Threats and Trends: What You Need to Know to Protect Your Data,” the top cyberrisks from 2014 and the first half of 2015 came from:
- attacks on point-of-sale (POS) systems
- banking trojans and downloaders
- various forms of hacktivism
- critical infrastructure attacks
- open-source software exploitation
- vulnerability research “crowdsourcing”
Check out the infographic below for some of the report’s key insights into the top cyberthreats and the biggest vulnerabilities for enterprise security: