Yesterday, at the Gartner Security & Risk Management Summit, I sat in on a session on advanced persistent response, presented by Tom Kellermann, vice president for cybersecurity, North America, for Trend Micro. Many of us are familiar with advance persistent threats, and to pay homage to the elite hackers of the world, in a way, the term advanced persistent response was coined.
Let us reflect on history. “There is a lot we can learn from Constantinople,” said Kellermann. “It was never defeated in battle until 1453. It demonstrated the fact that perimeter defenses were inefficient regarding onslaughts. Traditional internet security is insufficient. In fact, Trend Micro evaluations find over 90% of infrastructure is infected by malware.”
Kellermann noted that the cyber kill chain, or a set of sequential events that make up an advanced attack, has significantly evolved. The kills chain goes as follows:
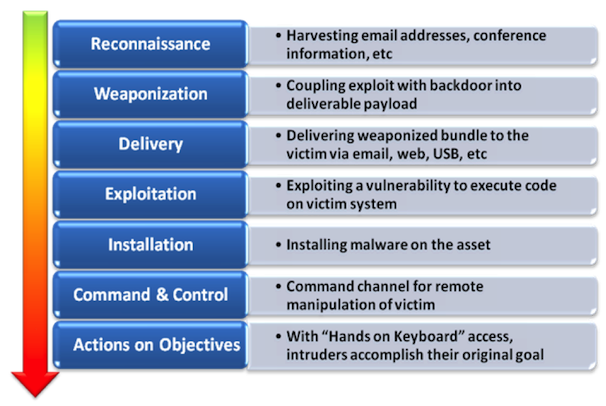
This year, an eighth stage has been added to the chain, known as the maintenance stage. “This eighth stage is due to hackers worrying about other hackers infiltrating the systems they have attacked more so than being woried about you,” said Kellermann. “We’ve noticed they’ve moved command and control into your systems and network. We really have to move beyond the technologies we’ve used for years and achieve advanced persistent response.”
Kellermann also acknowledged some emerging threats on the cyberwarfare landscape, including:
- professionalization and commoditization of exploit kits
- modularization
- increased sophistication with traffic direction systems
- ransomware
- new exploitation vectors introduced via html5
- evolution of mobile threats
- continued exploitation of social networks
- metasploit
- byod aka byom (bring your own malware)
He notes that although street crime is down 20%, that doesn’t mean there are less criminals, they’re just migrating to cyberspace. He points to Android malware and the fact that it “has exploded.” In a frightening example, he explains what cyber criminals are able to do with Androids now. “They can go into your phone and look at your calendar. They say, ‘I see on your calendar that you have a very important meeting on a certian day. During that meeting I’m going to turn on the microphone on your cell phone and at the same time hack into everyone’s phone who’s at that meeting.'”
As for Kellermann’s 2012 predictions, they aren’t pretty:
- mobile malware will continue to explode
- app attacks will increase
- botnet migration
- cloud attacks
- web injection attacks
This is serious information that every company must take into consideration. Not every organization will have to deal with advance persistent threats, but every organization should be prepared using the theory of advanced persistent response.
