A wide range of risks are trickling down from Russia’s assault on Ukraine, from sanctions compliance to supply chain disruption to business interruption. Cyberrisk has also drawn considerable concern and the threat landscape continues to evolve rapidly, though the details of increased cyberattack activity are not yet fully known and may be largely unfolding below the surface right now. Attacks attributed to Russia have been launched against a range of targets in Ukraine, including new destructive malware campaigns, targeted information-gathering against a range of civilian and government targets, and attacks on critical infrastructure.
Concerns about escalating cyber activity around the crisis are a vivid reminder of the importance of knowing your threat model and adjusting your risk management priorities accordingly. According to experts ranging from independent cybersecurity professionals to officials at the Cybersecurity and Infrastructure Security Agency (CISA), organizations at greatest risk right now include critical infrastructure, banks and other financial services firms, and of course key service providers in Ukraine or Russia.
Spill-over to other businesses is more likely with cyber conflict, however, particularly given Russia is one of the most advanced and aggressive nation-state cyber threat actors—remember the crippling global attack known as NotPetya that upended supply chains in 2017 resulted from a Russian cyberattack on Ukraine. That is not to say that there is necessarily cause for panic, simply that the effects of cyber conflict can be unexpected, widespread and potentially severe.
At this point, for most companies that are not in a high-risk position as a direct result of the war, the best course of action for risk professionals is to focus on ensuring your company has an updated and detailed incident response plan on hand and distributing it to relevant members of the organization, reviewing and potentially strengthening your general cybersecurity posture, and reminding employees about cyber hygiene.
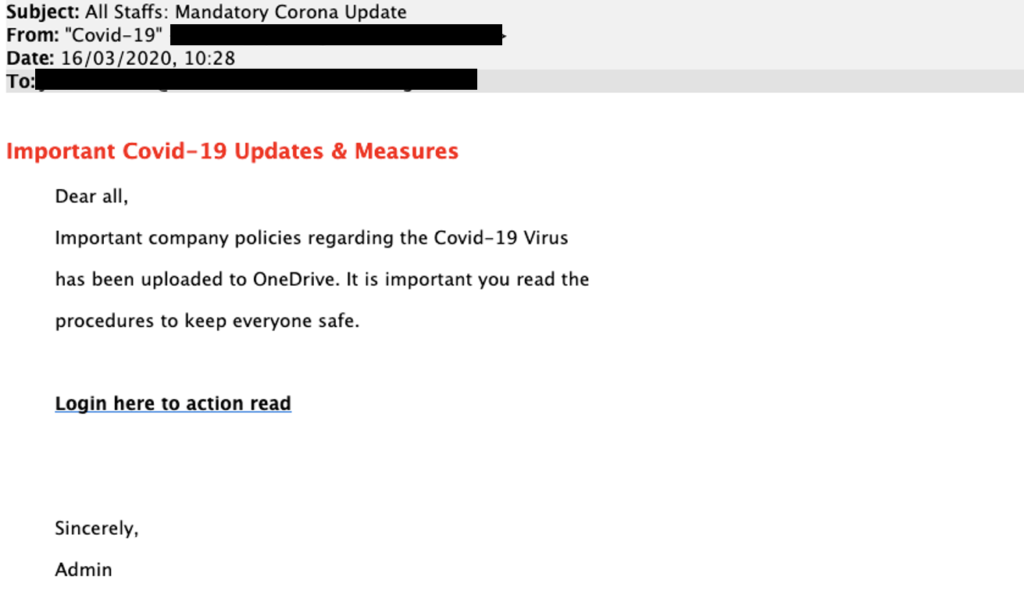
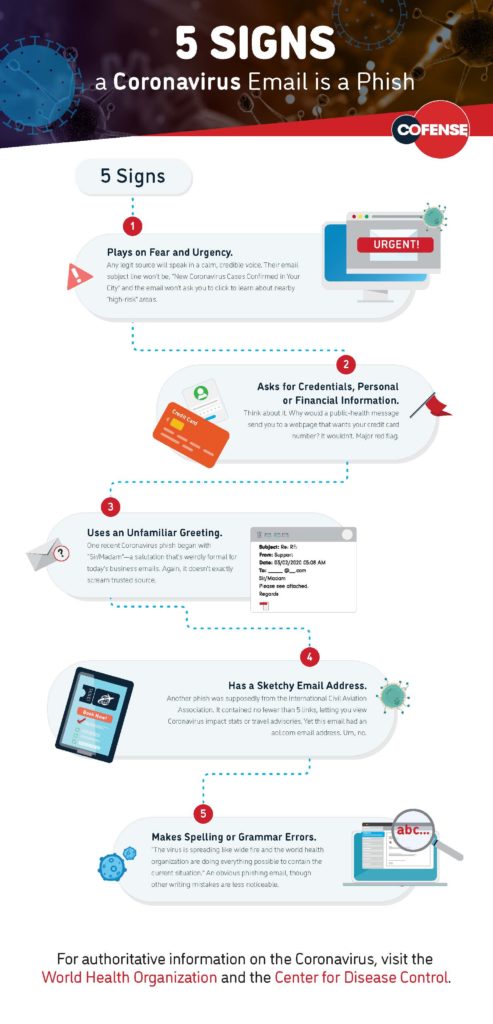
For example, given the tragic events and breaking developments around the conflict, many may be glued to news or social media. Unfortunately malicious actors are known to take advantage of such situations by posting phishing links on social media with alleged news updates or email scams that purport to collect charity donations. Remind employees about these perils and offer refreshers on how to spot phishing scams and the need to exercise caution with links in emails or on social media.
“In addition to taking a fresh look at plans and other policies within an organization’s cybersecurity risk framework, businesses should consider a few common-sense tips to prepare for a potential cyber incident,” advised Annmarie Giblin, partner at Hinshaw & Culbertson and leader of the firm’s data privacy and cybersecurity practice. Giblin recommended risk professionals take the following steps to boost cyberrisk management efforts right now:
- Print out a hard copy of any necessary polices and plans, like the cyber incident response plan, the business’ cyber insurance policy and a contact list for the organization, so you have them available in the event you cannot access your system and need to communicate with employees through alternative methods.
- Remind your employees about common cyber scams and reiterate that there will be no retaliation for reporting a cybersecurity mistake, such as clicking on a bad link.
- Have key members of the executive team and incident response team set up a secure but alternate method of communication, such as sharing phone numbers or creating a different off system email address to communicate in the event the business’ systems are not available or not trusted.
- Keep track of the latest threats and get the research over to your IT team so they can update your firewall, and/or contact the business’ security services provider and make sure they are aware of and addressing these new malware strains.
- Evaluate and if possible, test your business continuity plans. Organizations should be asking themselves, “What does the work day look like without access to the business’ systems?” and “How can we still work without any technology support?”
Cyber insurance firm Coalition has put together a guide to basic cybersecurity measures to help organizations—policyholders and otherwise—proactively manage cyberrisk and reduce the likelihood of a cybersecurity incident. The guide provides 10 key steps to help improve cyberrisk management, highlighting the basics of each mitigation measure, tips on how to implement, and even some vendor suggestions for credible options, if desired. Coalition notes this may be particularly helpful for small and mid-sized businesses that do not necessarily have dedicated in-house information security experts, but it could also be worth a look for any risk professional who wants an overview of mitigations that should be in place or ways to fill those gaps. Check it out here: https://info.coalitioninc.com/rs/566-KWJ-784/images/DLC-2020-12-2021-Coalition-Cybersecurity-Guide.pdf
For more resources on cyberrisk management best practices, cyber incident response, cyber insurance considerations, and more, check out Risk Management Magazine’s extensive cyber coverage here. Some of the highlights below can help address key concerns that you—or your board—may have right now, and offer actionable strategies to strengthen your cyberrisk readiness and boost employee cyber hygiene:
- What Are You Doing About Ransomware?
- A Crash Course in Data Breach Readiness
- Developing a Formal Cyber Incident Response Plan
- Cyber Risk Management in the Pandemic Era
- Cybersecurity Policies for Remote Work
- When Job Functions Are Not Cybersecure
- The Legal Issues in Cyber Incident Response
- Mitigating the Cybersecurity Risks of Remote Workers
- Fighting Coronavirus Phishing Scams
- Strengthening Third-Party Risk Management
- An Enterprise Approach to Data Security