Forecasting what the IT security landscape will look like in the year ahead has become an annual technology tradition, and following 2014 as the Year of the Data Breach, I think anyone could make a fairly accurate guess as to what the major trend of the New Year will be: more data breaches.
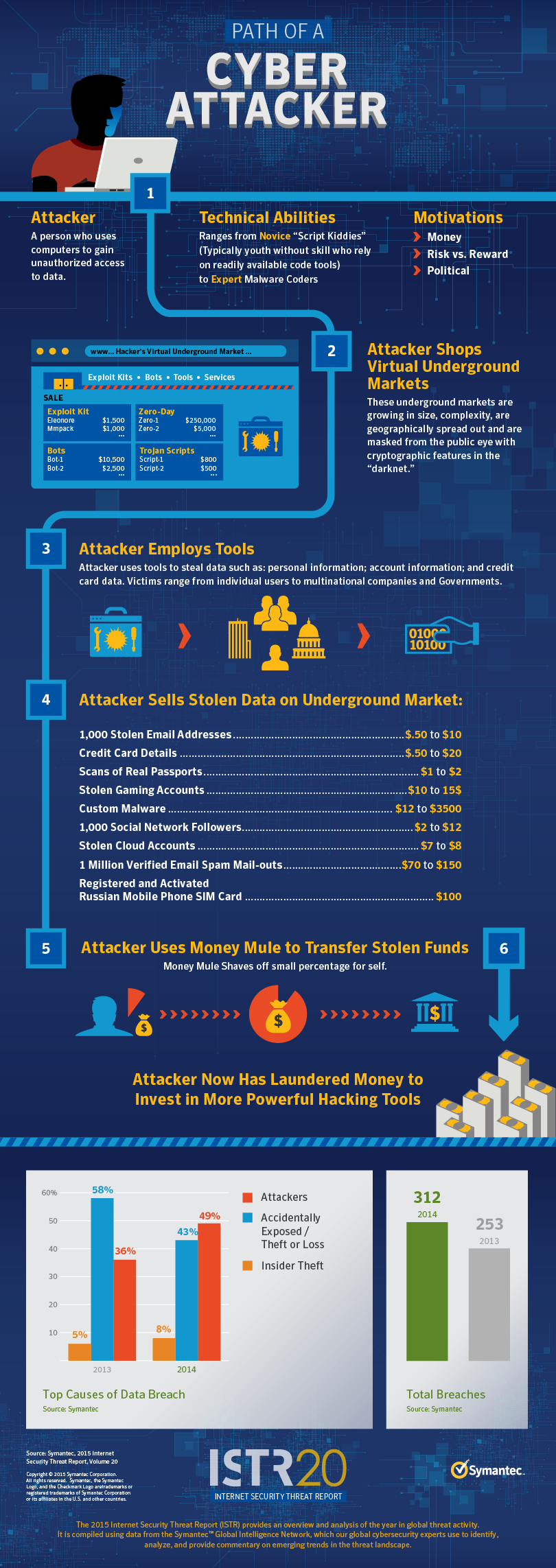
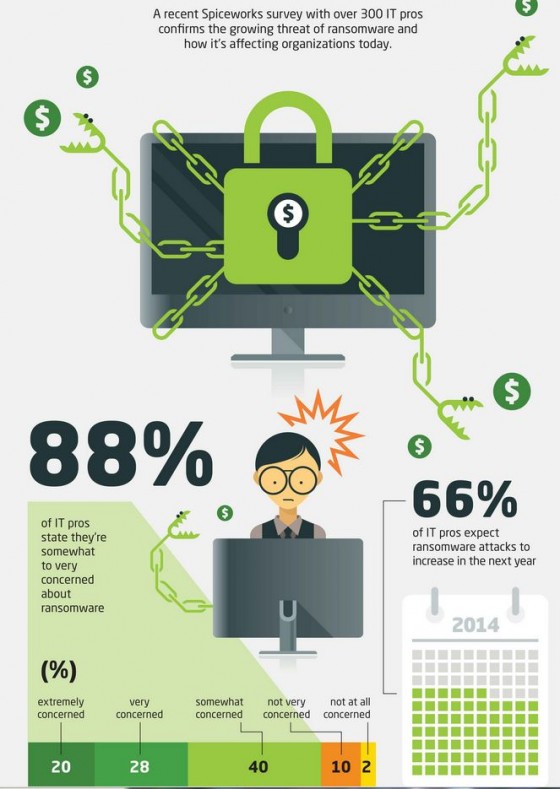
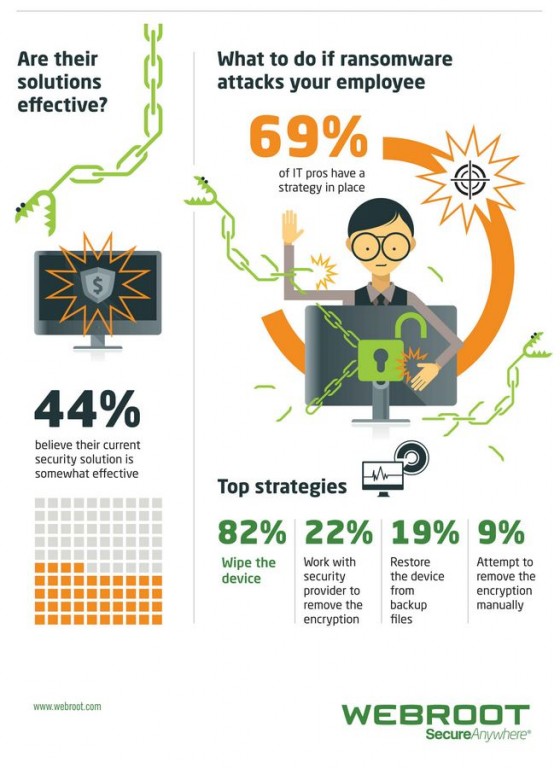
Forty-three percent of organizations reported a data breach in the past year, a figure that Forrester predicts will rise up to 60% in 2015. And it’s not just the frequency of breaches that we will see escalate in the year ahead, but also that malware will be increasingly difficult to dismantle. P2P, darknet and tor communications will become more prevalent, and forums selling malware and stolen data will retreat further into hidden corners of the Internet in an attempt to avoid infiltration.
By now, it is no longer a matter of if your business is going to be breached, but when. The last thing any organization needs as we enter another year of risk, is a blind side. The good news, though, is that there are ways to prevent them if we act immediately.
We know that an increase in cyber-attacks by stealthier hackers and more sophisticated malware is a sensible prediction – more important, now, is thinking about our resolutions, and how to prepare against what may be lurking ahead.
Here are my top New Year Resolutions for better enterprise security in 2015:
Layer Proactive Defenses
In 2014, many businesses were bitten by data breaches despite spending millions on state-of-the-art, next-generation solutions. In 2015, organizations will have to think smarter and build security from the ground up, layering defenses rather than relying on next-gen panaceas.
Furthermore, this kind of multi-layered approach should encompass more proactive measures – reactive “detective” tactics no longer cut it. Malware has always been hard to detect, and yet I see company after company relying too closely on detection technologies like antivirus (which, believe it or not, works only 50% of the time at best).
Lock Down Data
Following widespread data losses in 2014, businesses should resolve to lock down access to corporate systems and data. This starts with implementing greater control over user accounts and administrative privileges. Employees should always be logging onto systems as a standard user, and even then, businesses need to continue to control and monitor access to files and databases with active anomaly detection. Regular reviews of user roles and their access requirements should become a standard practice.
Ask More Questions
Heartbleed, Shellshock and recently, SChannel attacks have all shaken our confidence in common protocols that underpin much of the internet. Organizations need to practice greater scrutiny in evaluating what is offered by their selected vendors to ensure patching is swift and targeted. Far more questions should be asked around vendors’ processes for code auditing and testing.
Look to Two-Factor Authentication
Many of the attacks of 2014 could have been prevented by two-factor authentication, from the iCloud breach to the eBay compromise. Organizations should be looking to implement two-factor authentication as a way to prevent stolen or shared credentials being used against them. While this method is not a comprehensive solution to address all the security threats we’ll likely face, it does introduce a much needed layer of security.
Don’t Let Security Get in the Way
Stringent security practices are absolutely essential, but they can become a double-edged sword. Locking down system access for instance, although it significantly boosts the organization’s overall security posture, can strike a serious blow to end user productivity. Security must always be top of mind for IT organizations, but you’d be surprised at how quickly appetite to risk changes when its implementation reduces employees’ freedom and flexibility. Here is where deploying strategies like least privilege and sandboxing can have a significant impact by creating a productive and positive working experience for users, without compromising security.
In 2015, businesses should resolve to think smarter about their approach to security. It’s easy to become enamored by the latest glitzy perimeter solutions and invest heavily in next-gen antivirus and firewalls. But, making the most of those investments means thinking more strategically about how they can be layered with more proactive measures and additional safety nets to create a truly defense-in-depth framework. Most of all, we must strive to act on the greatest good principle. After all, IT isn’t the only business stakeholder, and finding a security solution that allows for a seamless user experience is what will most effectively drive adoption – and greater security success.