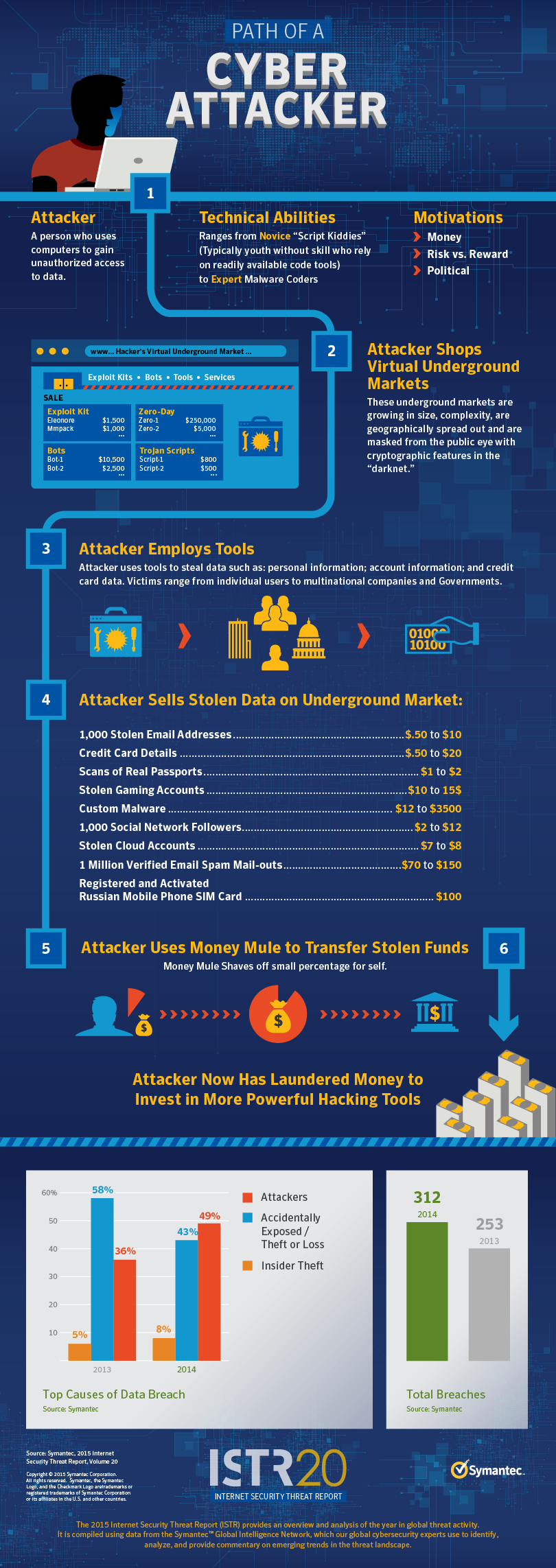
As cyberrisks evolve, enterprises have begun to focus on the insider threat by adding specialized capabilities for behavioral analytics on top of endpoint and network monitoring. In order for these tools to be most successful, there must be a fundamental understanding of the role an insider plays in a breach. Not every employee-caused breach is malicious, but they certainly are numerous. In fact, according to Verizon’s most recent Data Breach Investigation Report, 90% of breaches have a human component, regardless of intent.
Insider threats are a rampant problem exemplified by several recent headline-making incidents: the indictment of six Chinese nationals on suspicion of stealing intellectual property worth millions from two U.S. technology firms; accusations from financial giant Morgan Stanley toward an employee believed to have stolen client information with the intent to sell it; and claims from wearable-maker Jawbone that its competitor Fitbit regularly courted its privileged employees, enticing several of them to switch companies and bring sensitive details on its products. The uncertainty around all of these cases begs a couple of important questions: how can intent be determined, and how can employee privacy be maintained while ensuring business security?
Malicious or Careless?
Many think of insider threats only in terms of deliberate attacks, but the risk includes damage caused by simple carelessness. It is important to note the differences between malicious and careless incidents to ensure you are taking the right steps to mitigate the threat to your organization.
“Malicious incident” means an employee or someone trusted with network access has acted deliberately, either of their own volition or under the influence of others. A rogue malicious employee usually breaches security policy intentionally for personal gain. This type of incident is illustrated by the Jawbone/Fitbit controversy, as well as the case of the accused Chinese nationals mentioned above.
Three of those six individuals allegedly leveraged their positions at tech firms to steal research and technology they could replicate and profit from in China.
Conversely, the non-malicious insider threat often stems from employees’ inadvertent mistakes. There is no endgame, just a failure to follow security protocol. This can happen when employees breach policy intentionally but without malicious intent, not recognizing the risk. Sensitive data may be lost due to use of an unauthorized app (“shadow IT”) or manipulation through social engineering attacks, for example. This is easily the most common form of insider threat and can be seen in any case where employee credentials are stolen due to carelessness. To create a truly complete response plan to address insider threats, these incidents must be accounted for as well.
The Most Common Attack Vectors
Through our customer assessments, we have found that most threats stem from two common groups: employees who are planning on leaving the company, and privileged users who are targeted by outside actors.
We’ve come across employees attempting to steal sensitive information before leaving their employers a shocking number of times. In a large portion of investigations launched within three months of working with new customers, we’ve discovered employees attempting to leave with trade secrets that will help them down the road. In recent customer assessments, we found staff using hacking tools not required for their job—like Wireshark and Process Hacker —in two-thirds of cases, and we found staff actively bypassing company security measures 96% of the time.
But the bigger problem we have noticed is outsiders targeting privileged users in order to get into an organization’s networks. Attackers seek out privileged users in order to get quicker and deeper access to sensitive and strategically important information. It’s not as hard as you’d think; 75% of assessments found staff using pirated software, and 93% found sensitive information both in the cloud and on unencrypted USBs.
These risky practices open the door for phishing schemes, watering-hole attacks, and a slew of other approaches aimed at gaining access to user credentials. A growing number of these highly targeted forms of attack are being perpetrated by sophisticated, well-managed criminal organizations.
Don’t Compromise Privacy
Knowing the varying possibilities, organizations are hard-pressed to guarantee awareness of suspicious or dangerous activities without impacting their employees’ rights to privacy. To address this, start by focusing monitoring on rich, context-heavy data that truly describes typical workforce activity—for example, baseline user behavior over a set period of time to identify uncharacteristic access to sensitive data, running new and unusual applications, or downloading files that an employee has never touched before.
But don’t forget the need to protect the privacy of your employees. Conversations with the legal and HR departments are critical to ensure your plan abides by the legal and ethical limits on gaining insight into user activity.
Be sure the efforts to stamp out an insider threat don’t come at the expense of the rights of the rest of your workforce.
How Does This Affect the Enterprise?
Whether driven by a careless user, a disgruntled employee looking for quick monetary gain or state-backed espionage, insider threats can have a huge and devastating impact on an organization. Enterprises are beginning to realize they need to understand not only their networks and systems but also their employees and their activities. Historically, a majority of businesses ignored the issue. The most recent Vormetric Insider Threat Report shows 89% of organizations feel vulnerable to the risk of insider threats, but organizations taking a proactive approach still remain in the minority.
Your best bet is to adhere to the philosophy of “trust, but verify.” Rather than focus on locking down certain applications and limiting access to many or all users at the network perimeter, organizations must gain broad visibility into behavior across the company to identify the most pressing vulnerabilities. Not until that has become a widespread practice will enterprises have a true handle on the insider threat.