In a perfect cybersecurity world, people would only have access to the data they need, and only when they need it. However, IT budgets are tighter than ever and, in most organizations, manually updating new and existing employees’ access levels on a consistent basis is a time-consuming productivity-killer. As a result, there’s a good chance an employee may accidentally have access to a group of files that they should not. As one can imagine, security that is loosely managed across the enterprise is a breeding ground for malware.
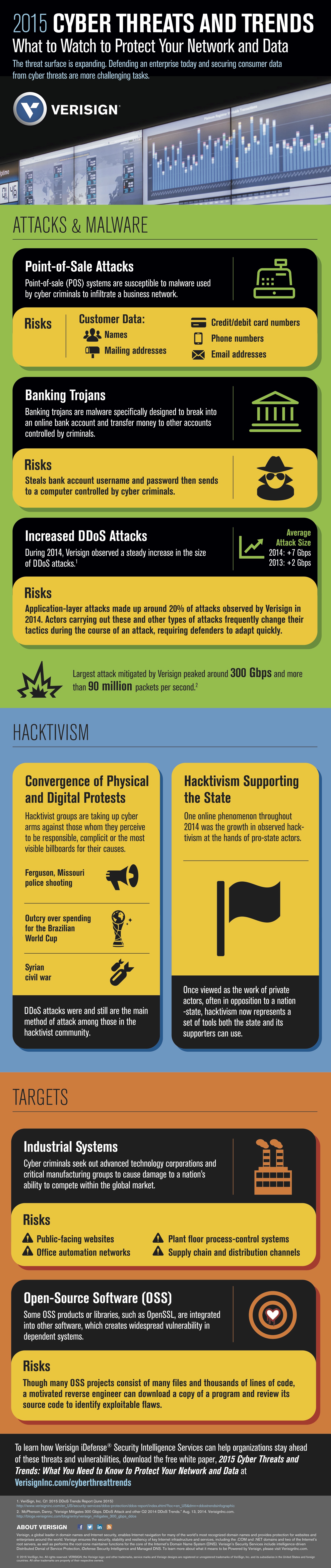
The velocity of cyberattacks has accelerated as well. It is easier than ever for cyber criminals to access exploits, malware, phishing tools, and other resources to automate the creation and execution of an attack. Digitization, Internet connectivity, and smart device growth are creating more vectors for attackers to gain an entry point into an organization’s network, and this trend only gets worse as you think about the Internet of Things, which could have concrete impact on machines from production equipment to planes and cars.
One way IT departments can help mitigate the cyberrisk of employee access overload is through automating security policies and processes such as the monitoring, detection and remediation of threats. In the past, organizations have spent a lot on prevention technologies: disparate point solutions such as anti-virus software and firewalls that try to act before an attack occurs. Prevention is important but not 100% effective. And how could technology used for prevention stop a cyber-attacker that has already infiltrated the network? If prevention were the end-all, be-all in security tools, we wouldn’t be reading about cyberattacks on a daily basis.
As more companies realize this, a spending shift to detection and response is being driven.
To help determine cyberrisk—or better yet, safely manage your cyberrisk—you must look at the threat (which is ever growing due to constant hackers and advanced techniques), vulnerability (how open your data is to cyberattacks), and consequence (the amount of time threats are doing damage in your network). Or, more simply put: risk = threat X vulnerability X consequence time.
To manage your cyberrisk, you need to optimize at least one of the aforementioned variables. Unfortunately, threat is the one variable that cannot be optimized because hackers will never stop attacking and are creating malware at an escalating rate. In fact, a G DATA study showed that 6 million new malware strains were found by researchers in 2014—almost double the number of new strains found the previous year. Instead, what organizations can focus on is investing in the right solutions that target the remaining two variables: vulnerability and consequence.
- Step One: Organizations must make sure they know their environments well (such as endpoints, network, and access points) and know where their sensitive information lives. It’s always a good idea to rank systems and information in terms of criticality, value and importance to the business.
buy cymbalta online shadidanin.com/wp-content/uploads/2023/10/jpg/cymbalta.html no prescription pharmacy
- Step Two: Organizations must gain increased visibility into potential threat activity occurring in the environment. As is often said, there are two types of companies: those that have been attacked and those that have been attacked and don’t know it. A way to increase visibility is through the deployment of behavior-based technology on the network, like sandboxes. Organizations are now shifting their focus to the endpoint. Today’s attacks require endpoint and network visibility, including correlation of this activity. The challenge with visibility is that it can be overwhelming.
- Step Three: There needs to be some process or mechanism to determine which alerts matter and which ones should be prioritized. In order to gain increased visibility into environments and detect today’s threats, organizations clearly need to deploy more contemporary detection solutions and advanced threat analytics.
- Step Four: Invest more in response and shift the mindset to continuous response. If attacks are continuous and we are continuously monitoring, then the next logical step is to respond continuously. Historically, response has been episodic or event-driven (“I’ve been attacked – Do something!
buy zithromax online shadidanin.com/wp-content/uploads/2023/10/jpg/zithromax.html no prescription pharmacy
”). This mindset needs to shift to continuous response (“I’m getting attacked all the time – Do something!”). A key ingredient to enable continuous incident response will be the increasing use of automation. Why? Automation is required to keep up with attackers that are leveraging automation to attack. It’s also required to address a key challenge that large and small companies face: the significant cybersecurity skills shortage.
Advanced threat analytics should be important to any organization that takes its security posture seriously. The majority of threats being faced today are getting more advanced by the minute. If an organization relies solely on legacy, signature-based detection, their defenses will be easily breached. It’s important for teams to understand that the cyber defense and response capabilities of an organization must constantly evolve to match the evolving threat landscape. This includes both automatic detection and remediation. Automatic remediation dramatically reduces the time that malware can exist on a network and also reduces the amount of time spent investigating the issue at hand. With automated security defenses, IT teams are given a forensic view of every packet that moves through the network and allows teams to spot anomalies and threats before they have a chance to wreak havoc. And since these tools are automated and work at machine speed, they can deal with a high volume of threats without necessitating human intervention, taking some of the load off overburdened security teams, and ultimately freeing them to act decisively and quickly, before network damage is done.