Rapidly developing computer technologies and the unrelenting evolution of cyberrisks present one of the biggest challenges to the (re)insurance sector today. Liabilities from cyberattacks and threats to the data security of cloud computing and social media have become key emerging risks for carriers. The unprecedented rise in cyberattacks, in addition to the threat cyberrisk poses to global supply chains, has seen the cyberinsurance market grow significantly in recent years.
Client demand for cyber coverage has been growing, on average, 30% annually in the United States over the past several years, according to Marsh. While demand varies by industry, the one constant has been that more clients are investigating and analyzing existing traditional insurance coverage and whether they need standalone cyberrisk insurance coverage.
Because cyberrisk is associated with the use of technology and the handling of all data and information, the threat transcends a company’s information technology (IT) department as well as what is confined to the internet. To help overcome some misconceptions that still exist for cyberrisks, some clarity around business exposures is needed to understand the scope of the threat.
Cyberattacks pose a danger to global supply chains
Cyberrisks are not isolated and are usually connected to other risks. Many companies that are exposed to cyberrisks are, for example, also exposed in turn to risks to their supply chain. Due to technological innovation and advances, many parts of a company’s or industry’s supply chain have become interconnected and automated.
Most commercial entities today are exposed to these risks as a growing number of businesses become more interconnected globally. A single cyberattack has the potential to put an entire company’s supply chain at risk. Therefore, cybersecurity and supply chain risk management must be considered in conjunction with one another.
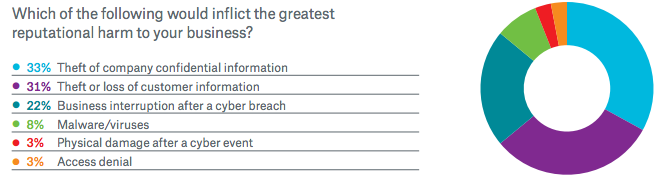
There are a range of risks when it comes to online/computer security. Cyberattacks can result in first party liability, including business interruption, computer security breaches, privacy breaches of confidential information and even third-party liability losses. Technology failures have begun to outpace adverse weather, fire and social unrest as the major force in disrupting a corporate supply chain, according to a recent Guy Carpenter report.
Everyone is at risk – individuals, companies and governments
In 2014, cyber issues have become more of a concern for companies that once felt they had relatively little exposure. In fact, cyberattacks were ranked fifth among the top five global risks in terms of likelihood in this year’s World Economic Forum’s annual Global Risks 2014 report.
Governments consider cyberattacks to be among the most serious economic and national security challenges now facing them. And through the ubiquitous use of the internet, mobile devices and social media, companies of all sizes and in all nations are now finding themselves at risk of falling prey to the full range of cyber perils. Such attacks can run from hackers shutting down a company’s network, gaining access to customers’ and employees’ personal and financial information, to the theft of business trade secrets.
More data laws and regulations in place
High-profile data breaches and other cybersecurity incidents have become more commonplace with increasingly onerous outcomes. Target, one of the largest retailers in the United States, suffered a massive cyberbreach late last year which involved the theft of approximately 40 million credit and debit card account details as well as personal data of nearly 70 million customers. The breach reportedly occurred when hackers used the retailer’s heating and cooling vendor’s system to navigate their way into the retailer’s records. The resulting publicity cost the company a significant amount in lost sales, loss of reputation, class action lawsuits, and may have contributed to the ouster of the chief executive officer. And most recently, a U.S.-based online auction site announced that hackers accessed the company’s 145 million user accounts and urged customers to change their passwords.
More recently, home improvement chain Home Depot became the victim of another credit card data breach and the FBI is reportedly investigating cyberattacks at some of the largest banks in the United States.
As cyber incidents affect both consumers and institutions, governments everywhere are putting more data privacy laws and regulations in place in regard to disclosure and other related safeguards. In the United States, there are laws that require the protection of both personal financial and health information. Last year, the U.S. Securities and Exchange Commission, which oversees publicly-traded companies, adopted a directive requiring certain regulated financial institutions and creditors to adopt and implement identity theft programs in light of the new cyber threats.
Risk mitigation and insurance
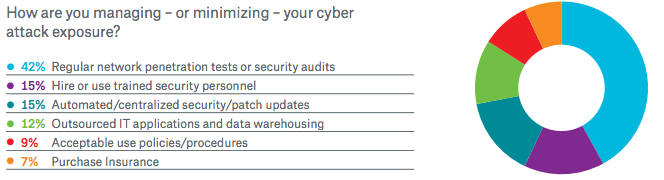
With governments considering and enacting new laws in response to the rising number of cyber events, companies, especially those in the United States, are taking a closer look at cyberrisk mitigation, including insurance coverage of breaches and attacks.
Media reports of serious data breaches have prompted more companies to buy cyber coverage of $100 million or more compared to the prior year, Marsh said in its March 2014 report Benchmarking Trends: Interest in Cyber Insurance Continues to Climb.
Traditional insurance products often do not cover risks that cover damages resulting from an incident like a computer breach.
As such, specific cyber liability insurance may be necessary.
The very process of applying for cyberrisk insurance is a constructive exercise for raising awareness and identifying potential vulnerabilities.
By engaging in that process, a company can perform a review of information security protocols with respect to access control, physical security, incident response and business continuity planning.
As a result, businesses and other institutions are finding that cyberinsurance products have been broadened to include coverage that now addresses nearly all aspects of technology-based risk faced by today’s companies. Carriers have been adapting their policies to include a variety of loss prevention and risk mitigation tools, ranging from turnkey breach response teams to pre-emptive risk analytics.
As cyberthreats become more severe, more frequent, and continue to change along with technological advances, the (re)insurance industry will continue to stay one step ahead by creating new forms of cyberrisk coverage to meet the needs of their clients.