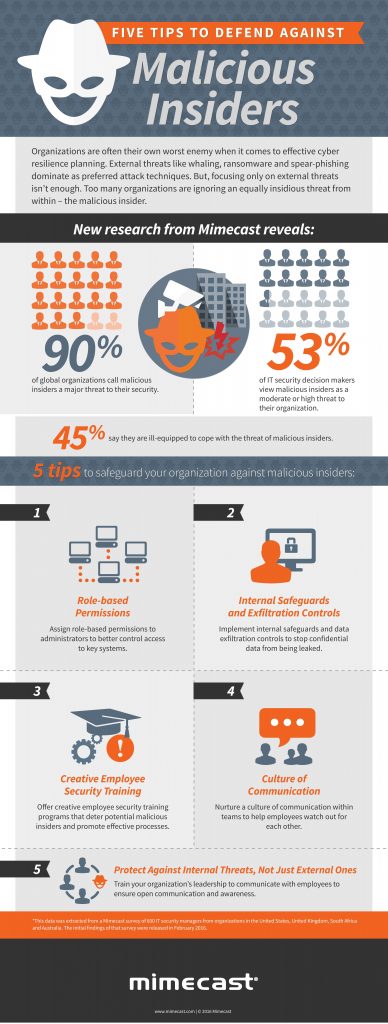
An overwhelming number of businesses increasingly see their greatest cyber threats coming from within, but figuring out what to do about the risk poses a formidable gap, according to a recent study from Mimecast. The email and data security company found that 90% of organizations globally consider malicious insiders a major threat to security, yet 45% report they are ill-equipped to cope with the risk. Indeed, one in seven IT security decision-makers view malicious insiders as their number one threat.
Current measures to guard against this risk may still leave significant exposure, and IT managers appear to know it. Those who say they are very equipped on cybersecurity feel virtually just as vulnerable to insider threats as those who believe they are not equipped at all (16% vs. 17%), “indicating that the risk of malicious insiders trumps perceptions of security confidence,” Mimecast reported.
Mimecast recommends the following strategies to guard against the risk of malicious insiders:
- Assign role-based permissions to administrators to better control access to key systems and limit the ability of a malicious insider to act.
- Implement internal safeguards and data exfiltration control to detect and mitigate the risk of malicious insiders when they do strike, to cut off their ability to send confidential data outside the network.
- Offer creative employee security training programs that deter potential malicious insiders in the first place and help others to spot the signs so they can report inappropriate activity to their managers. Then, back that up with effective processes to police and act swiftly in the event of an attack.
online pharmacy zyprexa with best prices today in the USA
- Nurture a culture of communication within teams to help employees watch out for each other and step in when someone seems like they’ve become disenchanted or are at risk of turning against the company.
- Train your organization’s leadership to communicate with employees to ensure open communication and awareness.
Check out more of the study’s findings in the infographic below:
Similar Posts:
- Improving IT Training Makes Cyberrisk Every Employee’s Responsibility
- Automation: The Key to More Effective Cyberrisk Management
- A Risk-Based Approach to Rating and Correcting Individual Cyberrisk
- Organizational Complexity Poses Critical Cyberrisk
- Cyberrisk Management Tips for Businesses Amid the Russia-Ukraine War