Ransomware attacks constituted the greatest cybercrime danger in 2016 as the volume and value of attacks rose sharply, according to a new report from internet security firm Symantec.
“Attackers have honed and perfected the ransomware business model, using strong encryption, anonymous Bitcoin payments, and vast spam campaigns to create dangerous and wide-ranging malware,” according to “Internet Security Threat Report (ISTR), April 2017.”
The average ransom amount involved in such attacks jumped 266% to $1,077 during 2016 from just $294 in 2015. Symantec also found that frequency increased, with detection of ransomware up 36% to 463,000 from 340,000 in 2015; or 1,271 per day in 2016 compared to 933 per day in 2015.
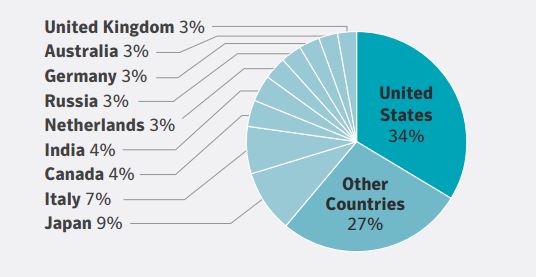
The United States saw the largest share of these attacks by far at 34%, followed by Japan (9%) and Italy (7%). “The statistics indicate that attackers are largely concentrating their efforts on developed, stable economies,” Symantec said. Further, research from Norton Cyber Security Insight team said that 34% of those attacked will pay the ransom, but that figure jumps to 64% for U.S. victims, “providing some indication as to why the country is so heavily targeted,” the Symantec report said.
Another indicator of rising ransomware activity is the tripling of new families of ransomware to 101 in 2016 from just 30 in both 2105 and 2014. While the number of new variants (distinct variants of existing ransomware families) declined 29% to 241,000 from 342,000 in 2015, this “suggests that more attackers are opting to start with a clean slate by creating a new family of ransomware rather than tweaking existing families by creating new variants,” the report said.
The proportion of ransomware infections on consumer computers rose only marginally to 69% from 67% in 2015 as the rate of infections for enterprise and other organizations dropped accordingly to 31% from 33% in 2015. Consumer infections totaled between 59% and 79% for every month except December, when they fell to 51%.
Beyond the top threat of ransomware, the report discusses exposures including “New frontiers: Internet of Things, mobile, & cloud threats,” and has a section that lists multiple challenges from malware, spam and phishing via email. Email, for example, was a major avenue of attack in 2016, “used by everyone from state- sponsored cyber espionage groups to mass-mailing ransomware gangs,” it said, adding that one in 131 sent during 2016 were malicious, the highest incidence in five years.
Symantec also discusses a few of the largest cybercrimes of the year, including the theft of $81 million from the central bank of Bangladesh and alleged tampering with the U.S. electoral process. “Cyber attackers revealed new levels of ambition in 2016, a year marked by extraordinary attacks, including multi-million dollar virtual bank heists, overt attempts to disrupt the US electoral process by state-sponsored groups, and some of the biggest distributed denial of service (DDoS) attacks on record,” according to the report.
Despite the apparent rising threat level portrayed in the report, the cyber insurance landscape remains untamed, Risk Management Magazine reported in April. Potential customers would be wise to educate themselves prior to approaching the market.