The investigation into a huge cyberattack on JP Morgan Chase last year has exposed one of the largest computer hacking and fraud schemes to date.
online pharmacy
periactin with best prices today in the USA
According to U.S. prosecutors, Gery Shalon, Joshua Samuel Aaron and Ziv Orenstein, all from Israel, hacked a total of 12 companies to expose the personal information of more than 100 million people, netting hundreds of millions of dollars in profit. The men face 23 criminal counts, including wire fraud, computer hacking, illegal internet gambling and money laundering, with alleged crimes targeting 12 companies, including nine financial services companies and media outlets including the Wall Street Journal. Investigators say their massive criminal empire used 75 shell companies that employed hundreds of people, and hacked seven major banks, ran an online casino, laundered money around the world and set up an illegal Bitcoin trading operation.
online pharmacy
zestril with best prices today in the USA
“It is hacking in support of a diversified criminal conglomerate,” said Preet Bharara, U.S. attorney for the Southern District of New York. “In short, it is hacking as a business model.”
In addition to the hack of JP Morgan, which U.S. Attorney General Loretta Lynch called “the largest theft of customer data from a U.S. financial institution” and exposed the personal information of 83 million customers, the criminals also attacked E*Trade Financial Corp., TD Ameritrade, Scottrade Inc., Fidelity Investments and News Corp’s Dow Jones, which publishes the Wall Street Journal. The breaches date as far back as 2007.
“By any measure, the data breaches at these firms were breathtaking in scope and in size,” Bharara said. “This showcases a brave new world of hacking for profit.”
Breaking into these financial institutions gave the attackers information to target specific people, and gave them extra insight into the stock market. According to the indictment, they used the customer data to contact individuals and push them to buy stocks in order to manipulate their prices. In addition to the pump-and-dump scheme, sometimes the defendants reportedly engineered mergers with shell companies to create publicly traded stocks that could be manipulated.
online pharmacy
symbicort with best prices today in the USA
Bharara called the scheme “securities fraud on cyber steroids.”
Beginning in 2012, in addition to disguising payments and constantly obtaining new bank accounts, the men further tried to evade detection by hacking into a company that assessed merchant risk for credit-card issuers. The breach allowed the defendants to read employees’ emails and figure out how to sidestep the company’s efforts to monitor illegal payments, according to the indictment.
The defendants are also accused of operating at least 12 illegal internet casinos, even launching cyberattacks against rival gambling businesses to review executives’ email and gain a competitive edge. Shalon hacked competitors’ customer databases and directed denial of service attacks to shut down their businesses.
Several compliance officers may soon feel the heat as well: the investigation found that, in operating the online casinos and illegal pharmaceutical payment processing enterprises, the co-conspirators deceived financial institutions into processing and authorizing payments between the casino companies and others. “They colluded with corrupt international bank officials who willfully ignored its criminal nature in order to profit from, as a co-conspirator described it to Shalon, their payment processing ‘casino/software/pharmaceutical cocktail’,” the indictment charges.
According to prosecutors, the case illustrates the growing power of criminals and their tools, and makes such crimes particularly difficult to solve. But it may also highlight one key resource to do so: self-reporting to law enforcement. Officials credited JP Morgan’s early cooperation for helping to uncover the network of criminal activity. The firm came forward early on to share information with the government, a move many forensic investigators encourage.
buy prednisone online https://galenapharm.com/pharmacy/prednisone.html no prescription
This case provides one of the clearest examples of why: hackers frequently use the same schemes to target a swath of companies in a given industry. While many companies worry about the reputational and regulatory risks of disclosing a breach to law enforcement, as hackers grow more sophisticated in their techniques and complex in their operations, it may prove an ever more critical step in the breach response and investigation process.
“Shalon, Aaron, and their co-conspirators allegedly robbed victim companies, often for months at a time, stealing the contact information of tens of millions of customers,” said FBI Assistant Director-in-Charge Diego Rodriguez. “They cloaked themselves in secrecy, but their methods rivaled those of the traditional masked robber. Today’s indictment sheds light on an increasingly complex threat. But just as criminals continue to develop relationships with one another in order to advance their objectives, the law enforcement community has developed a collaborative approach to fighting these types of crimes.”
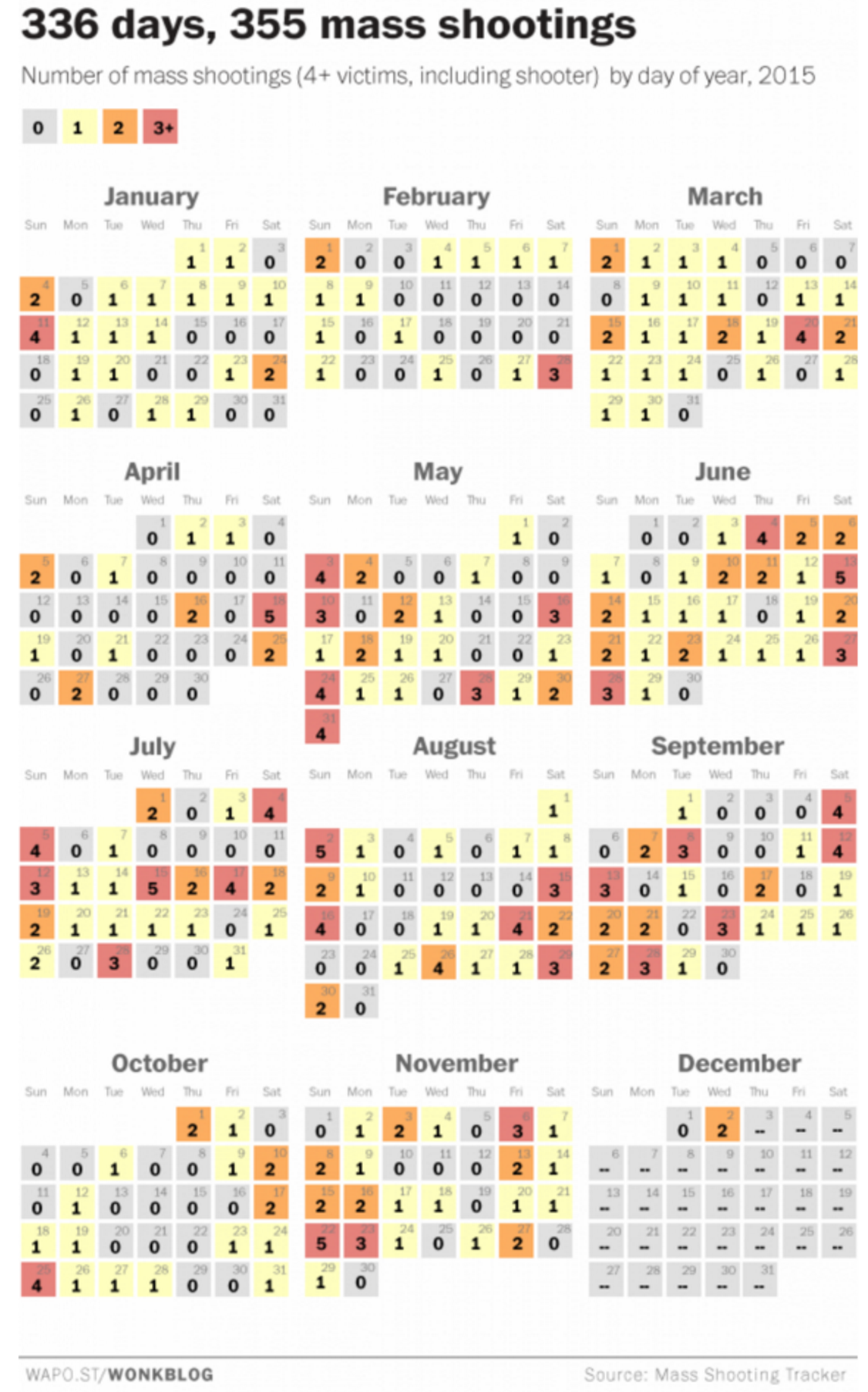 Yesterday, Dec. 2, 2015, marked the 336th day of the year and 355th mass shooting, according to the Mass Shooting Tracker, which logs incidents in which four or more people are shot. Indeed, there were two mass shootings yesterday: a smaller incident in Georgia in which a woman was killed and three men injured, and the slaughter of at least 14 people and injury of 17 at an office holiday party at San Bernadino’s Inland Regional Center, which provides social services to residents with developmental disabilities. No motive has been found thus far, but two shooters have been identified as a county employee who had attended the party and his wife.
Yesterday, Dec. 2, 2015, marked the 336th day of the year and 355th mass shooting, according to the Mass Shooting Tracker, which logs incidents in which four or more people are shot. Indeed, there were two mass shootings yesterday: a smaller incident in Georgia in which a woman was killed and three men injured, and the slaughter of at least 14 people and injury of 17 at an office holiday party at San Bernadino’s Inland Regional Center, which provides social services to residents with developmental disabilities. No motive has been found thus far, but two shooters have been identified as a county employee who had attended the party and his wife.