Last year was certainly a turning point in the history of online privacy and cyber security. Between ransomware attacks, the Equifax breach and the Federal Communication Commission’s vote to repeal net neutrality regulations—just to name a few high-profile incidents in the United States—businesses and citizens have more reasons than ever to safeguard their information.
To address this important issue, the annual Data Privacy Day (DPD) will be held Jan. 28, with online and in-person events leading up to it now that celebrate individual users’ rights to privacy and aim to prevent cyber theft and risk. DPD has been led by the National Cyber Security Alliance (NCSA) in the U.S. since 2011 and “highlights our ever-more connected lives and the critical roles consumers and businesses play in protecting personal information and online privacy,” said NCSA Executive Director Michael Kaiser.
DPD was created to commemorate the 1981 signing of Convention 108 by the Council of Europe and is observed by more than 47 countries. It was the first legally binding international treaty dealing with privacy and data protection and officially recognized privacy as a human right. NCSA also co-hosts National Cybersecurity Awareness Month and the Department of Homeland Security’s Stop.Think.Connect. campaign, which aims to increase the public’s understanding of cyber threats.
“Our personal information and our habits and interests fuel the next generation of technological advancement, like the Internet of Things, which will connect devices in our homes, schools and workplaces,” Kaiser said. “Consumers must learn how best to protect their information and businesses must ensure that they are transparent about the ways they handle and protect personal information.”
 On Jan. 25, LinkedIn will live-stream an event from its San Francisco office exploring the theme of “Respecting Privacy, Safeguarding Data and Enabling Trust.” The broadcast will feature TED-style talks and panel discussions with experts focusing on the pressing issues that affect businesses and consumers. Additional DPD happenings include Twitter chats and networking gatherings to maintain a dialogue about the importance of privacy rights.
On Jan. 25, LinkedIn will live-stream an event from its San Francisco office exploring the theme of “Respecting Privacy, Safeguarding Data and Enabling Trust.” The broadcast will feature TED-style talks and panel discussions with experts focusing on the pressing issues that affect businesses and consumers. Additional DPD happenings include Twitter chats and networking gatherings to maintain a dialogue about the importance of privacy rights.
 The relevance does not end on Jan. 29, noted Richard Purcell, DPD advisory board member and chief executive officer of Corporate Privacy Group. He has witnessed the event’s evolution and its impact on risk management and privacy professionals.
The relevance does not end on Jan. 29, noted Richard Purcell, DPD advisory board member and chief executive officer of Corporate Privacy Group. He has witnessed the event’s evolution and its impact on risk management and privacy professionals.
“The community of privacy professionals is not made up of private people. They want to share information,” noted Purcell, who was named Microsoft’s first corporate privacy officer in 2000. “They initiate a dialogue that the officers bring back to their companies. I have seen how it has stimulated events inside corporations and universities that were inspired by Data Privacy Day networking discussions. The professional development aspects of the day are profound.”
 Newly released information from NCSA demonstrates how privacy is impacted in both personal and professional environments—from healthcare and retail to social media, home devices and parenting. Some statistics include:
Newly released information from NCSA demonstrates how privacy is impacted in both personal and professional environments—from healthcare and retail to social media, home devices and parenting. Some statistics include:
- In 2016, 2.2 billion data records were compromised and vulnerabilities were uncovered in internet of things products from leading brands.
- 41% of Americans have been personally subjected to harassing behavior online and nearly one in five (18%) has been subjected to particularly severe forms of harassment online, such as physical threats, harassment over a sustained period, sexual harassment or stalking.
- Nearly one-third of consumers do not know that many of the “free” online services they use are paid for via targeted advertising made possible by the tracking and collecting of their personal data.
- About 78% of respondents to a recent survey of healthcare professionals said they have had either a malware and/or ransomware attack in the last 12 months.

 5. In fact, not only is failing to prepare for an attack or breach risky, it’s foolish, Kathleen McGee, internet & technology bureau chief for the Office of the Attorney General of the State of New York said in Monday’s opening address. She added that not reporting a breach in a timely fashion has its own set of legal and reputational risks, referring to
5. In fact, not only is failing to prepare for an attack or breach risky, it’s foolish, Kathleen McGee, internet & technology bureau chief for the Office of the Attorney General of the State of New York said in Monday’s opening address. She added that not reporting a breach in a timely fashion has its own set of legal and reputational risks, referring to 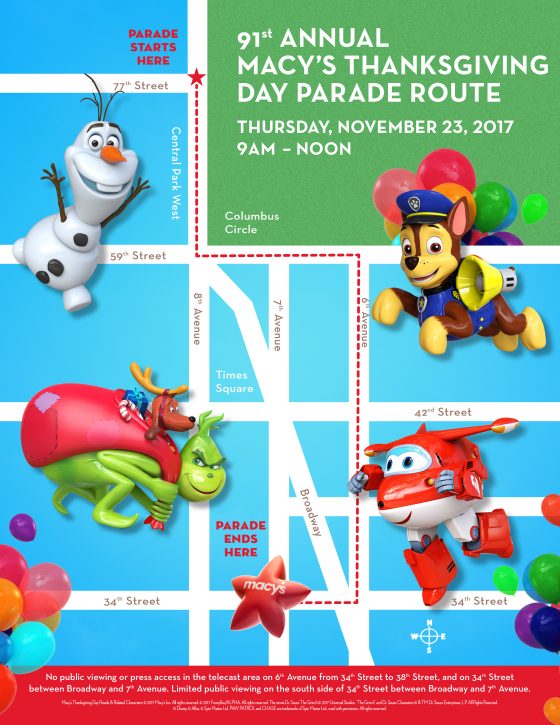 Theresa Morzello, the managing director for asset services for CBRE in New York City, has advised many companies who stay open or host events coinciding with parades and holidays. She said the first steps in mitigating disruption involve communicating with the event organizers and disseminating that information to tenants.
Theresa Morzello, the managing director for asset services for CBRE in New York City, has advised many companies who stay open or host events coinciding with parades and holidays. She said the first steps in mitigating disruption involve communicating with the event organizers and disseminating that information to tenants.