The International Labour Organization estimates that 25 million people are subject to human trafficking around the world, with children comprising one of every four victims. In many cases, the victims are used and transported by their traffickers in supply chains.
Tim Nelson is the international development director for Hope For Justice, an anti-trafficking organization that aims to end modern slavery. He also holds the same title at the Slave-Free Alliance, an affiliated group that collaborates with businesses to assess and prevent the risk of human trafficking in their supply chains. Nelson recently appeared on RIMScast to discuss the how human trafficking has evolved into a major supply chain risk and how employers and employees can identify signs of this abuse.
Check out some highlights below, and to take a free deep-dive with Nelson and learn how to take action to prevent human trafficking in your company and community, download RIMScast episode 120.
For more information on steps businesses should take to help identify and combat modern slavery on their premises, you can also check out the Risk Management feature article “Human Trafficking: How Businesses Can Combat the Modern Slavery Epidemic.”
What inspired the creation of the Slave-Free Alliance?
Tim Nelson: We primarily started in the U.K., and formed because of the Modern Slavery Act, which requires companies with £36 million (about $50 million) or more in their annual revenue to state their efforts to remove slavery from their supply chain. Consequently, we tend to work with businesses above that £36 million level and we try and effectively help them honor their commitment.
We also work alongside federal or local police and alongside other NGOs and effectively try and be a trusted friend. Many people, because of the countries that they come from or what they’ve been told, are suspicious of police or are worried about corruption. We can be there to build that bridge of trust.
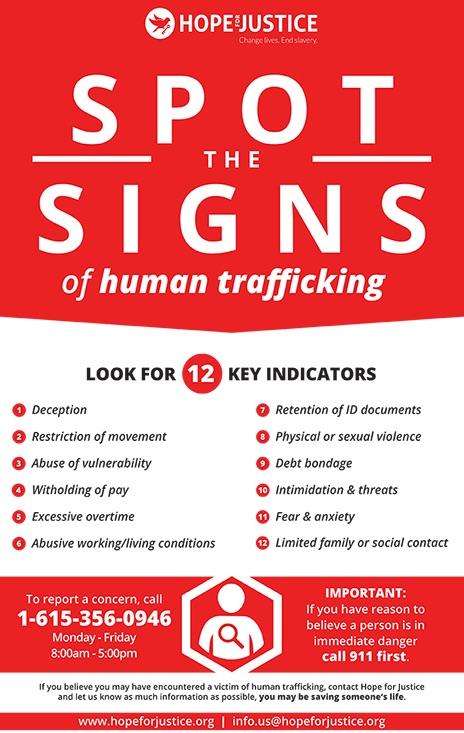
How can someone identify trafficking and modern slavery?
TN: Traffickers are those individuals who would use other people to generate profit for themselves and are looking for every opportunity. Global estimates indicate that there’s $150 billion made from this illegal activity. And therefore, the traffickers have thought it through.
One of the complexities in identifying it is that human trafficking is hidden in plain sight. The common form that most people are aware of is sexual exploitation. But ultimately, traffickers [also] realized that they could traffic individuals to work in the supply chains of businesses, making components, working in manufacturing, working in agriculture.
Could you provide an example of how traffickers permeate supply chains?
TN: Last year there was a case where 400 victims were identified as being slaves within the primary supply chain of some of the major supermarkets within the U.K. And, like we said earlier, it was in plain sight—no one could see how this was happening.
This particular occurrence happened because the traffickers had gotten control of a recruitment company and they were able to bring individuals from a non-English-speaking nation to the U.K. Those individuals were given jobs, but the traffickers had control of their bank accounts. They were forcing these 30-plus individuals to live in a three-bedroom property. Many of them were washing themselves in a local river—not having running water was a sign that this is not how people should be living in 2020.
National Slavery & Human Trafficking Prevention Month is held annually in January to educate about the different forms of human trafficking. What can risk professionals do to ensure the awareness continues all year?
TN: I would encourage all businesses to realize that they’ve got the power to change this so easily if they start to engage and put in different processes and systems. And part of what we’re trying to do is not to just encourage individuals or companies to stop buying goods from a particular company. If you just stop dealing with a company because you suspect there’s modern day slavery or trafficking happening, that company will close and another one will open like a phoenix. Companies can also sometimes be complicit just by not even looking or allowing enough due diligence to show that they are slave-free within the supply chain.
Is there a bottom-line impact as well?
TN: What we are seeing now is, internationally, inaction can be a major risk to your business. I can think of companies where issues around slavery were brought to the fore and share prices dropped by half as institutional investors pulled out. This is a key ESG issue, which makes it a C-suite-level risk in many cases.
What should companies expect when they engage with the Slave-Free Alliance?
TN: The first thing that we would do is conduct a gap analysis. This is not just looking at where you’re getting supply from—it’s to try and identify the weaknesses that may be in your supply chain. And that gap analysis forms something almost like a risk register.
Every company is different. I spoke to a Fortune 100 company last month that didn’t even have a procurement division. And that’s what I would have assumed every major multinational had. But every company has a different approach to it.
Quite often, a lot of people find that the even the thought of how big their supply chain creates a massive complexity because there might be just three people running the procurement department.
When we see something that would sit within the risks that we identify, then we work with the companies to diminish that risk. It could be an [unannounced] site assessment or working with those people who are going in and auditing the factories themselves.

